
Beyond our ability to provide comprehensive technical support services, one of the most important ways that Banshee Networks distinguishes itself is in our ability to provide value to our clients by delivering high-level analysis of organizations’ stated goals, policies and processes in relation to their actual Information Technology (IT) infrastructure and regulatory requirements in order to provide recommendations for process improvement:
When a client engages us for this service, our first action is to examine the functional aspects of their organization to determine if there are any significant IT liabilities that may be present, identify any technical economies-of-scale that may be leveraged to improve efficiencies/reduce operating costs and evaluate processes to see how well they mesh with the current IT infrastructure and capabilities. Further, based upon the analysis that is performed, when a client determines that there are areas that require change we assist by creating a “road-map” to clearly identify the necessary actions and costs to implement such changes. At a high-level, this comprehensive process helps us answer the following important questions for your organization:
-
Do your technology-related systems, policies and procedures mesh with the current technical requirements and the stated goals of the organization?
-
Is your organization complying with applicable regulation, with regard to IT standards, that may apply to your industry (ISO, PCI, HIPAA, Sarbanes-Oxley, etc.)?
-
Does your organization have adequate technology to provide comprehensive, threat management against corporate espionage, cyber-crime or cyber-attacks? How would you know if your company’s most important secrets were stolen or someone was in the act of trying to steal them?
-
Has your organization identified and weighed all the risks that could seriously threaten operations so that corresponding mitigation can be implemented to proactively address each?
-
Does your organization employ an effective incident response plan to minimize your liability, maximize business continuity and mitigate damages in the event that a breach of security or a loss of confidential information does occur?
-
Does your organization have a disaster recovery plan and does this plan meet the sustainability and timing requirements (recovery point and time objectives or RPO/RTO) of the business?
-
Is your organization’s confidential IT information secure and are policies and procedures fully documented and agreed to by your employees?
-
Is your company’s IT infrastructure optimized, efficient and in conformance with security standards and regulation?
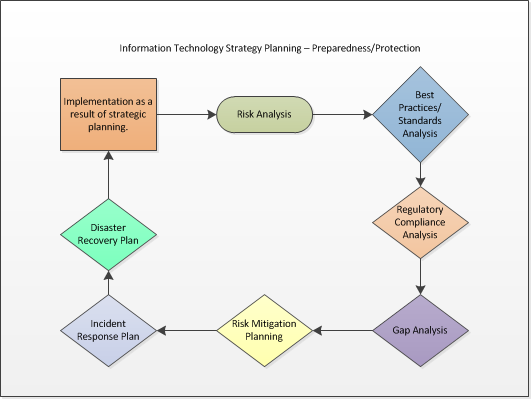
The strategic planning process is ongoing and results in our providing a “living,” planning document that is continuously updated as variables within the organization change. Regular reviews allow us to comprehensively revisit and reevaluate the overall IT strategy in order to help proactively identify new technical goals, determine how to effectively mitigate identified risks, assist in planning future projects that will help the organization to stay in conformance with the stated plan while meeting emerging technical requirements and regulation. Additional, tactical system reviews ensure that the information systems are meeting the goals of the overall, strategic plan and risks of obsolescence, operational problems, capacity issues or non-conformity with organizational security policy are identified and reported along with recommended solutions.
Our goal is to ensure that our clients not only enjoy the troubleshooting and implementation capabilities of a skilled, technical-support organization, but that they are also able to fully leverage the knowledge of an IT partner that can work with them to limit negative exposure, while also assisting in the future planning of IT systems and processes which are, for most organizations, the heart of the core organizational functions. While meeting the aforementioned goals, this comprehensive approach to service also enables us to share our experience and provide a deeper level of technical insight and awareness to our clients.
Small Business ServicesMidsized Business ServicesEnterprise Business ServicesWireless ServicesComputer ForensicsRegulatory Compliance/Industry Standards AssessmentCyber SecurityNetwork Management & Advanced TroubleshootingNetwork Penetration TestingCloud ServicesMobile SolutionsServices OverviewTechnologiesAbout
